Presentations

2026
From Application to Access: Detecting DPRK IT Workers Before They Become Insider Threats
BSides Seattle | 25min Track 3
How to detect and prevent DPRK IT Workers from being hired in your organization.

2025
Zero Budget Threat Intelligence
BSides Tokyo | Lightning Talk
How different security functions can easily operationalize threat intelligence at no additional cost.
2022
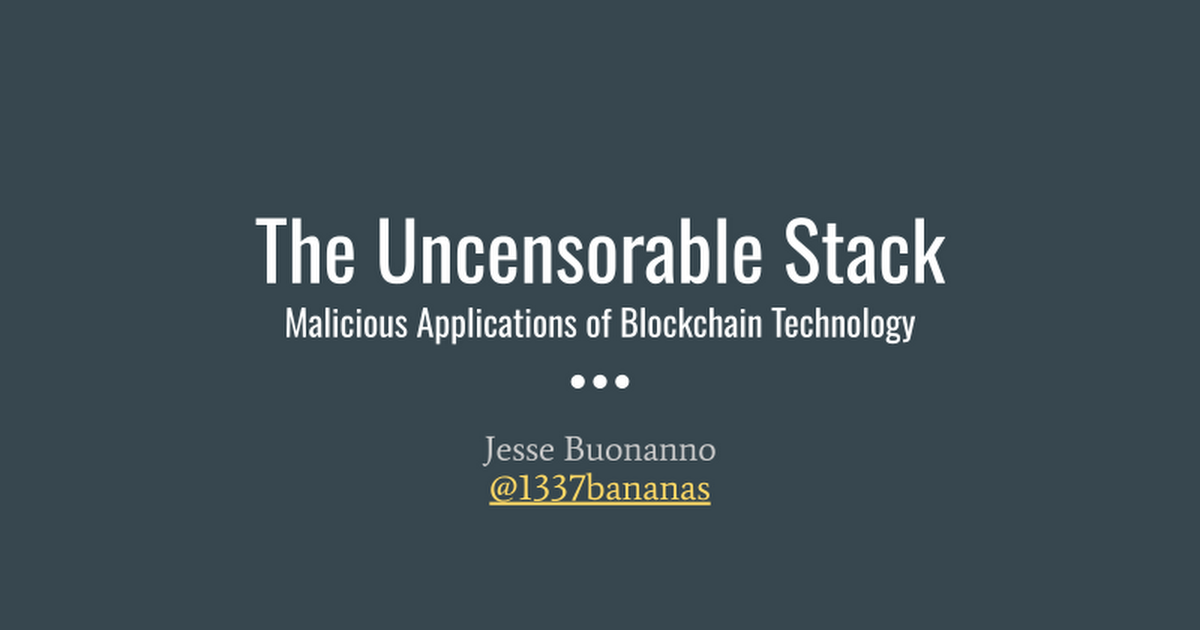
Malicious Applications of Blockchain Technology
BSides Charm & SANS Blockchain Security Summit
Blockchain technology introduces new opportunities for adversaries to level up their tradecraft. By combining different decentralized technologies full censorship resistant user-friendly applications can be built without a single point of failure. This talk will cover known attacker instances of blockchain based capabilities, dive into each layer of an uncensorable tech stack, demo what a malicious application might look like, and provide defenders mitigation strategies.